There are many WLAN adapter on the market that has the option of running in monitor mode. The TP-Link TL-WN722N WLAN adapter is one of the more accessible and cheap adapters in Scandinavia. Unfortunately, it's a bit of a pain to get up and running in Kali Linux. Especially the versions you can buy in stores today (v2/v3).
In this article, I will guide you through the process of installing the needed kernel module, and making it run in monitor mode in Kali Linux on a Virtual Machine in VirtualBox.
Enable adapter in VM
Make the Wi-Fi adapter accessable in the VM
Before the adapter can be used by Kali Linux, the adapter has to be enabled or attached to the VM. Open the settings for the VM, navigate to the USB menu, and add the Wi-Fi adapter to the VM. This way only the VM will be able to use the Wi-Fi adapter, and no other VM or your host OS.
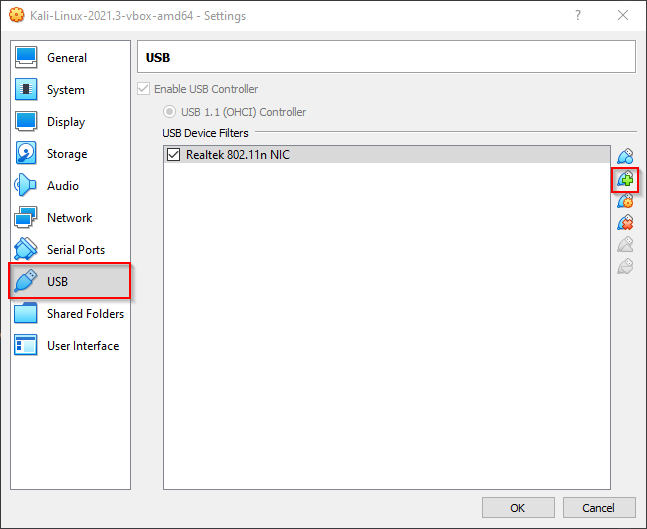
Add the Wi-Fi NIC to the Kali Linux Virtual Machine
To make the adapter appear in the VM you might have to restart it. To check if it's available you run the iwconfig command. If it's discovered by the Operating System it will appear in the output.
iwconfig
lo no wireless extensions.
eth0 no wireless extensions.
wlan0 IEEE 802.11g ESSID:"haxor"
Mode:Managed Frequency:2.427 GHz Access Point: 00:0D:9D:FF:FF:FF
Bit Rate=48 Mb/s Tx-Power=20 dBm Sensitivity=8/0
Retry limit:7 RTS thr:off Fragment thr:off
Power Management:off
Link Quality=91/100 Signal level=-39 dBm Noise level=-87 dBm
Rx invalid nwid:0 Rx invalid crypt:860 Rx invalid frag:0
Tx excessive retries:0 Invalid misc:39 Missed beacon:8As you can see from the output above the adapter was discovered. To enable monitor mode and start using it for ethical hacking you need to install a custom kernel module, and enable monitor mode.
Kernel module
Install the needed packages for your Kali VM
Before anything can be done, you need to have a fully updated version of Kali Linux. In my experience, the 2021 versions of Kali Linux do not break during updates. But proceed with caution! You might not be as lucky. Your best bet might be to download the newest VirtualBox image and proceed from there. To update Kali run these commands.
sudo apt update
sudo apt upgradeNow you must install the Linux kernel header files and the bc programming language packet. Both are necessary dependencies that are needed to compile the driver for the Wi-Fi adapter.
sudo apt install linux-headers-amd64
sudo apt install bcBefore we can use the new driver we must blacklist the default realtech kernel module (driver). To do this you first need to login as the root user. Please note that this is not possible to do with sudo privileges.
sudo su -Once logged in as root you can blacklist the kernel module.
echo "blacklist r8188eu" > "/etc/modprobe.d/realtek.conf"
exitNow you are ready to download the sourcecode to the custom kernel modules for the Wi-Fi adapter.
cd ~/Downloads
git clone https://github.com/aircrack-ng/rtl8188eus
cd rtl8188eusOnce downloaded you can compile the kernel module and install it.
make
sudo make install
sudo modprobe rtl8188eusAfter the installation, you can use the Wi-Fi adapter for ethical hacking.
WLAN sniffing
Make sure the adapter is running the new kernel module run this command
sudo airmon-ng
PHY Interface Driver Chipset
phy0 wlan0 8188eu TP-Link TL-WN722N v2/v3 [Realtek RTL8188EUS]As you can see from the output - the kernel module was successfully installed and running. To enable monitor mode on the adapter run this command:
sudo airmon-ng --verbose start wlan0
Found 2 processes that could cause trouble.
Kill them using 'airmon-ng check kill' before putting
the card in monitor mode, they will interfere by changing channels
and sometimes putting the interface back in managed mode
PID Name
485 NetworkManager
3847 wpa_supplicant
No LSB modules are available.
Distributor ID: Kali
Description: Kali GNU/Linux Rolling
Release: 2021.4
Codename: kali-rolling
Linux kali 5.14.0-kali4-amd64 #1 SMP Debian 5.14.16-1kali1 (2021-11-05) x86_64 GNU/Linux
Regulatory Domain appears to be unset, please consider setting it with 'iw reg set XX'
https://wireless.wiki.kernel.org/en/users/documentation/iw#updating_your_regulatory_domain
Detected VM using lspci
This appears to be a VirtualBox Virtual Machine
If your system supports VT-d, it may be possible to use PCI devices
If your system does not support VT-d, you can only use USB wifi cards
K indicates driver is from 5.14.0-kali4-amd64
V indicates driver comes directly from the vendor, almost certainly a bad thing
S indicates driver comes from the staging tree, these drivers are meant for reference not actual use, BEWARE
? indicates we do not know where the driver comes from... report this
X[PHY]Interface Driver[Stack]-FirmwareRev Chipset Extended Info
K[phy0]wlan0 8188eu[mac80211]-unavailable TP-Link TL-WN722N v2/v3 [Realtek RTL8188EUS] mode managed
(monitor mode enabled)From the verbose output for the command, you can see that it got activated in monitor mode. Another method of verifying that it is running in monitor mode is to run iwconfig:
iwconfig
lo no wireless extensions.
eth0 no wireless extensions.
wlan0 unassociated Nickname:"<WIFI@REALTEK>"
Mode:Monitor Frequency=2.457 GHz Access Point: Not-Associated
Sensitivity:0/0
Retry:off RTS thr:off Fragment thr:off
Power Management:off
Link Quality=0/100 Signal level=0 dBm Noise level=0 dBm
Rx invalid nwid:0 Rx invalid crypt:0 Rx invalid frag:0
Tx excessive retries:0 Invalid misc:0 Missed beacon:0As you can see from the output - the NIC is in monitor mode. You are now able to use it with wireshark and a lot of other fun networking tools. As a starter you can start running scan for access points and endpoints using airodump-ng:
sudo airodump-ng wlan0
CH 13 ][ Elapsed: 36 s ][ 2021-12-12 16:48
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID
72:02:71:7C:FF:FF -82 5 0 0 9 130 WPA2 CCMP PSK Victim_AP_01
72:02:71:7C:FF:FF -69 16 0 0 1 130 WPA2 CCMP PSK Victim_AP_02
50:C7:BF:4F:FF:FF -57 15 2 0 9 405 WPA2 CCMP PSK Victim_AP_03
BSSID STATION PWR Rate Lost Frames Notes Probes
(not associated) 7E:45:E3:FF:FF:FF -38 0 - 5 0 3 Victim_AP_04The Wi-Fi sniffer program airodump-ng will listen in on every channel looking for access points and devices. After a couple of minutes, you should have a list of all devices in the area. If you were able to successfully run airodump-ng using the Wi-Fi adapter you have verified that monitor mode is working correctly.
Congratulations. You now have a working Wi-Fi packet sniffing solution using the TP-Link TL-WN722N. Now, go ahead and use this for good!